The MCP Blindspot
Why standard AI servers fail at Zero Trust and how Self-Healing Auth fixes the Model Context Protocol security gap.
Welcome to Day 13 of #30DaysOfTrust.
The MCP Blindspot: Why Standard AI Servers Fail at Zero Trust 🧩🛡️
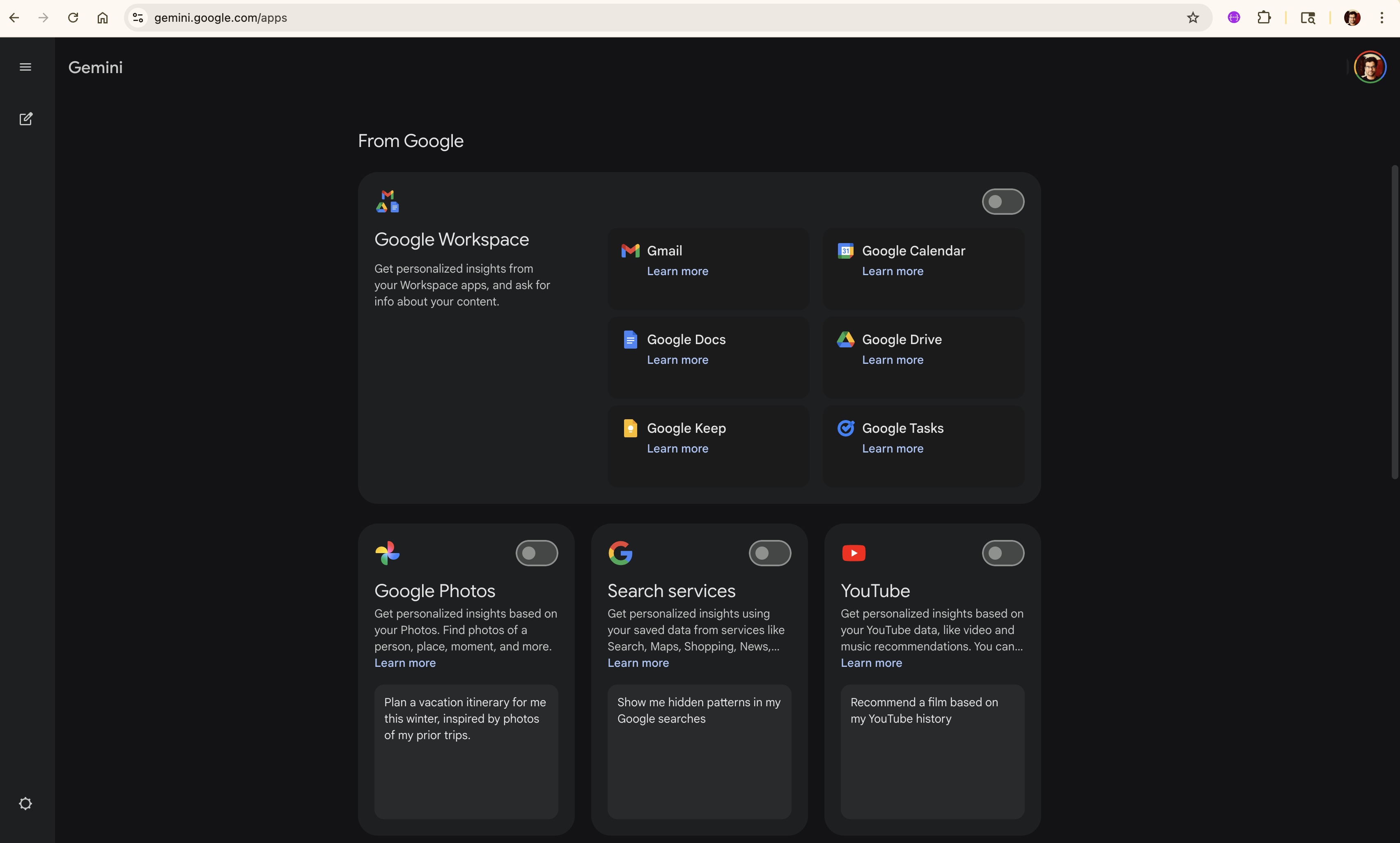
Take a look at the settings page for AI assistants like Google Gemini. To get personalized help, users are presented with a series of master switches. Want your AI to draft an email based on one specific document? You have to toggle on access to your entire Google Workspace—Gmail, Drive, Docs, Calendar, and everything in between.
This forces users into a state of "Allow All" anxiety before the AI has even executed a single task. In the enterprise landscape, we call this the "God Mode" problem. It completely breaks the fundamental security rule of Least Privilege.
The Zero Trust Gap in Model Context Protocol (MCP) 🚨
As the Model Context Protocol (MCP) becomes the standard for connecting LLMs to external tools, a massive blindspot has emerged. By design, MCP explicitly does not enforce security at the protocol level. It leaves authorization entirely up to the developer.
Because building dynamic, granular authorization is incredibly complex, the current market standard is a dangerous shortcut. Most MCP servers are deployed using over-permissioned, standing credentials. The AI agent starts its life holding the master keys to the database, just in case it needs them.
If an agent actually tries to use a tool without the right permissions, standard MCP servers hit a brick wall. They throw a 401 Unauthorized error, the agent hallucinates or crashes, and the developer's workflow is broken.
Bridging the Gap with "Self-Healing Auth" 🌉
We cannot expect enterprises to adopt autonomous agents if the prerequisite is sweeping, unchecked access. The solution lies in shifting from upfront bulk permissions to Just-In-Time (JIT) Authorization.
At SecuriX, we provide the infrastructure for developers to easily implement a frictionless flow we call Self-Healing Auth:
- 🛡️ Zero Trust Start: The AI agent boots up with zero access to external SaaS tools or private data.
- 🔫 The Trigger: A user prompts the agent to perform an action, such as summarizing a specific sales report from a CRM.
- 🔗 The Dynamic Consent: Instead of crashing with a 401 error because it lacks permission, our Trust Layer intercepts the tool call. The system pauses the agent's execution and generates a secure, dynamic consent URL directly within the chat interface.
- 🎫 The Guest Pass: The user clicks the link, authenticates, and grants access only for that specific tool call. The agent seamlessly resumes its thought process and completes the task.
Building Trust Through Infrastructure 🏗️
You aren't giving the AI the code to your safe; you are handing it a temporary guest pass to a single room, exactly when it needs it.
For teams building the next generation of B2B AI tools, hardcoding these granular authorization flows is a massive drain on resources. SecuriX provides the infrastructure to make Self-Healing Auth the default behavior. By treating authorization as a dynamic conversation rather than a static settings page, developers can build enterprise-ready tools that users inherently trust.
#30DaysOfTrust #MCP #ZeroTrust #AgenticAI #SelfHealingAuth #CyberSecurity #SecuriX #BuildInPublic #AIInfrastructure
Spread the word
Join the Agentic Revolution.
Build secure AI agents with the first-ever Agent Access Security Broker (AASB).
Start BuildingCommunity Forum
Questions, Feedback & Discussions
Join the conversation
Recent Discussions 0 Comments
No questions yet. Be the first!