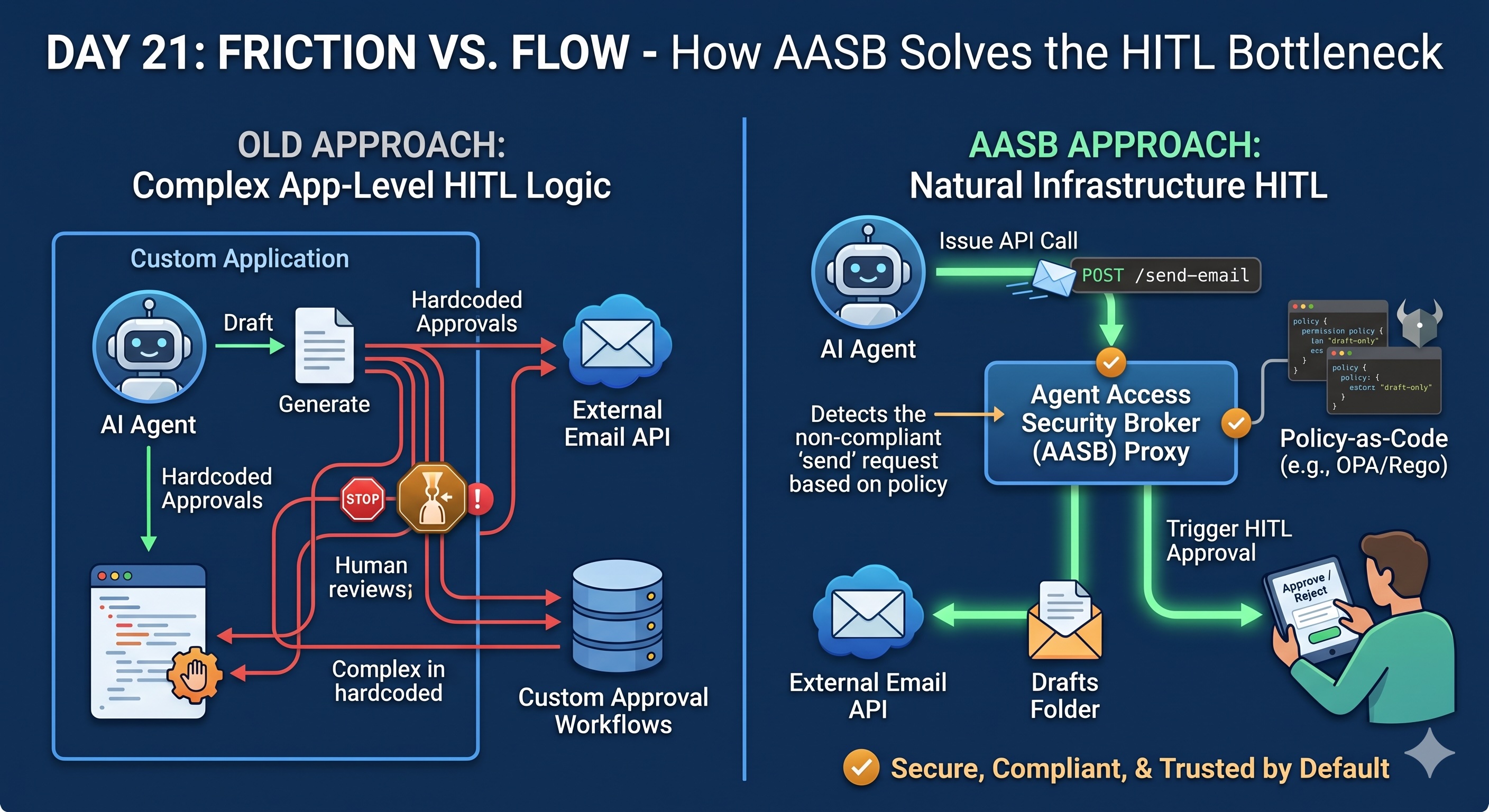
How AASB Infrastructure Solves the HITL Bottleneck
Learn how an Agent Access Security Broker (AASB) simplifies Human-in-the-Loop (HITL) workflows by handling oversight at the infrastructure layer instead of the application layer.
Welcome to Day 21 of our #30DaysOfTrust Challenge!
Yesterday, we established that autonomous AI needs supervision. Implementing a Human-in-the-Loop (HITL) workflow is non-negotiable for enterprises prioritizing "Trust by Default."
But this raises a massive challenge for developers: How do you introduce human oversight without bottlenecking your AI or hardcoding approval buttons into every single application?
If every AI interaction requires custom logic to pause, alert a human, and resume, development grinds to a halt. The solution isn't to build HITL into the app itself—the solution is to handle it at the infrastructure layer using an Agent Access Security Broker (AASB).
The AASB: Your Centralized HITL Proxy 🛡️🏢
An AASB acts as a proxy-level broker sitting between your AI agents and your enterprise data sources. Because all traffic routes through this single checkpoint, introducing HITL becomes a natural, friction-free process for the developer.
Instead of writing complex app-level code, you manage HITL through Policy-as-Code. You define the data boundaries once, and the infrastructure enforces them everywhere.
How AASB Automates the "Pause" ⏸️🤖
Let’s look at a practical B2B scenario: managing an AI agent that handles email communications.
A common requirement is allowing an AI to draft responses, but never letting it send an email without human review. The problem? Native OAuth does not support "Draft-Only" email scopes. If you grant an AI access to an inbox via standard OAuth, it often gets full send privileges by default.
This is where the AASB steps in to naturally execute a HITL workflow:
- The Policy: You deploy a centralized policy (using frameworks like OPA/Rego) stating that the AI agent only has "Draft" permissions.
- The Interception: The AI drafts the email perfectly. But if the agent attempts to execute a "Send" API call, the AASB proxy intercepts it.
- The Handoff: The broker automatically blocks the unauthorized action and routes the payload to a human operator for review.
The AI agent doesn't need to know it was paused, and the developer didn't have to write a custom "Draft-Only" workaround into the application layer. The infrastructure simply enforced the boundary.
Friction Where It Matters, Flow Everywhere Else 🌊🔒
By shifting HITL to a B2B infrastructure API, you achieve the perfect balance of friction and flow. Low-risk actions (like pulling a public summary) flow continuously. High-risk actions (like modifying a database or sending an external communication) hit the secure proxy and trigger a human review.
Developers get to focus on building brilliant AI agents, while the AASB silently ensures those agents remain secure, compliant, and trustworthy by default.
#30DaysOfTrust #HITL #AASB #AISecurity #AgentSecurity #PolicyAsCode #SecuriX #BuildInPublic #AIInfrastructure
Spread the word
Join the Agentic Revolution.
Build secure AI agents with the first-ever Agent Access Security Broker (AASB).
Start BuildingCommunity Forum
Questions, Feedback & Discussions
Join the conversation
Recent Discussions 0 Comments
No questions yet. Be the first!