The Evolution of AI Consumption
Moving from chatbots to Agent-as-a-Service (AaaS) and the new security frontier of autonomous AI.
Welcome to Day 6 of #30DaysOfTrust.
The Evolution of AI Consumption and the Next Security Frontier
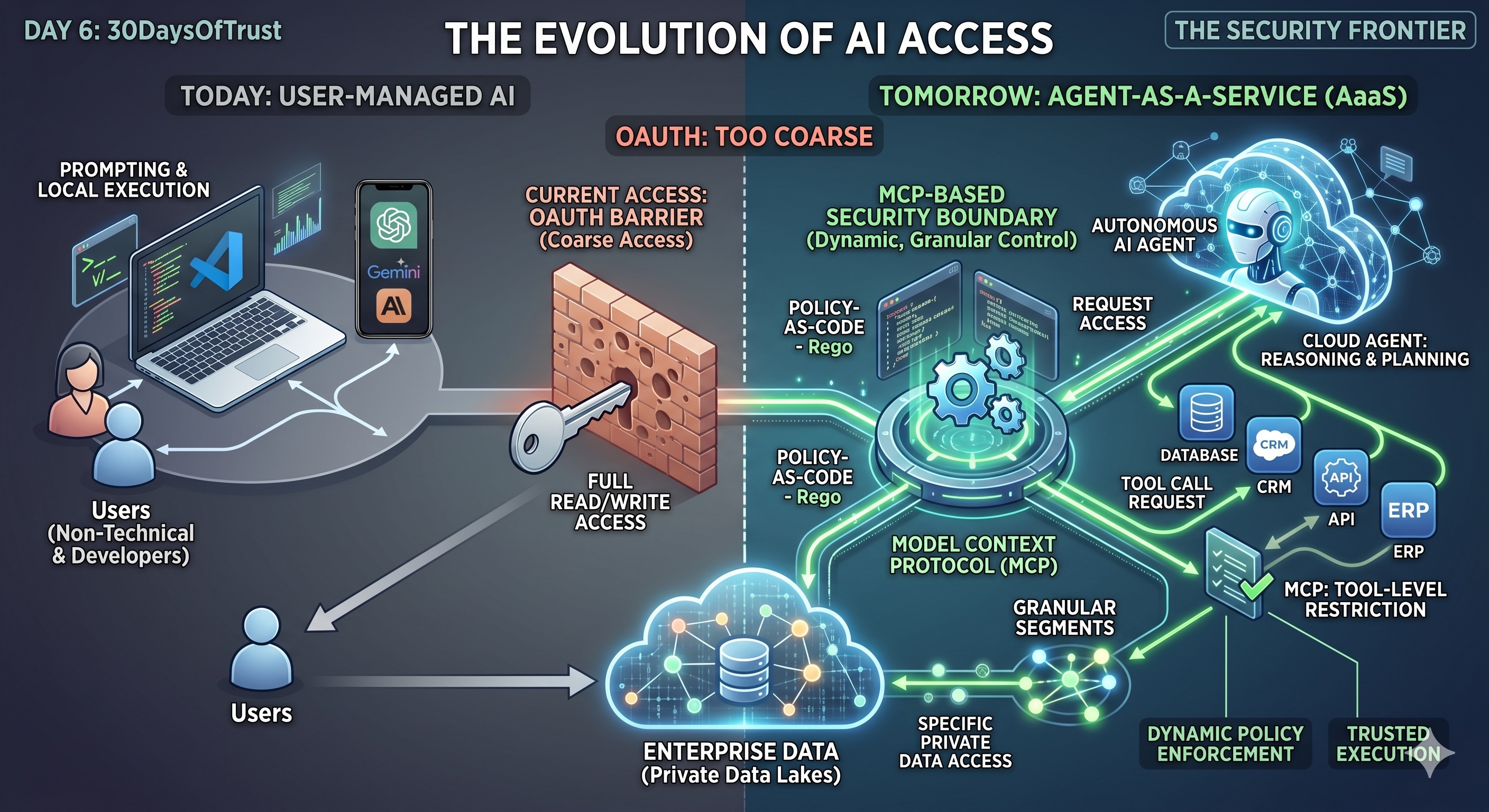
If you look at how users and enterprises interact with AI today, the landscape is heavily consolidated. The vast majority of consumption happens through conversational chatbots like Gemini, ChatGPT, and Claude. The remaining solo enthusiasts are leveraging coding agents locally within their IDEs.
But the paradigm is shifting rapidly.
The future is Agent-as-a-Service (AaaS). We are moving away from prompting chatbots toward deploying autonomous AI agents in the cloud—agents capable of reasoning, planning, and executing tasks against private enterprise data.
With this autonomy comes a massive shift in how we must approach security and trust.
🔒 The Autonomy Dilemma: Identity vs. Access
Historically, we’ve relied on OAuth to manage access. But for autonomous agents operating without a human-in-the-loop, OAuth alone is fundamentally too coarse. OAuth is necessary to prove on whose behalf an agent is acting, but granting an agent broad "read/write" tokens to an entire enterprise suite is a massive vulnerability.
Identity gets the agent to the door; we need a new way to dictate exactly what files and data it can touch once inside.
🛠️ The Solution: Tool-Level Boundaries & Policy-as-Code
As these agents operate in the cloud, their primary mechanism for accessing data and executing actions will be through designated tools via Model Context Protocols (MCPs).
This is where the new enterprise security boundary must be established.
- Single-Point Restriction: Instead of broad identity-based scopes, we must intercept and govern agent behavior directly at the MCP tool-execution layer.
- Dynamic Authorization: Hardcoding restrictions won't scale. We need context-aware evaluations using Policy-as-Code to check an agent's intent in real-time before allowing execution.
- Developer-First Infrastructure: Building this secure plumbing from scratch is a massive bottleneck. To accelerate AaaS, developers need plug-and-play trust layers that route tool calls through a secure broker, freeing them from building complex authorization engines themselves.
To build trust in the AaaS era, we have to move beyond coarse access tokens and start securing the very tools our agents use to interact with the world.
#30DaysOfTrust #AI #CyberSecurity #AgentAsAService #MachineLearning #EnterpriseTech #DataSecurity #TechInnovation #SecuriX #AgenticEra
Spread the word
Join the Agentic Revolution.
Build secure AI agents with the first-ever Agent Access Security Broker (AASB).
Start BuildingCommunity Forum
Questions, Feedback & Discussions
Join the conversation
Recent Discussions 0 Comments
No questions yet. Be the first!