Why 'Secure MCP' is the Future of AI Trust
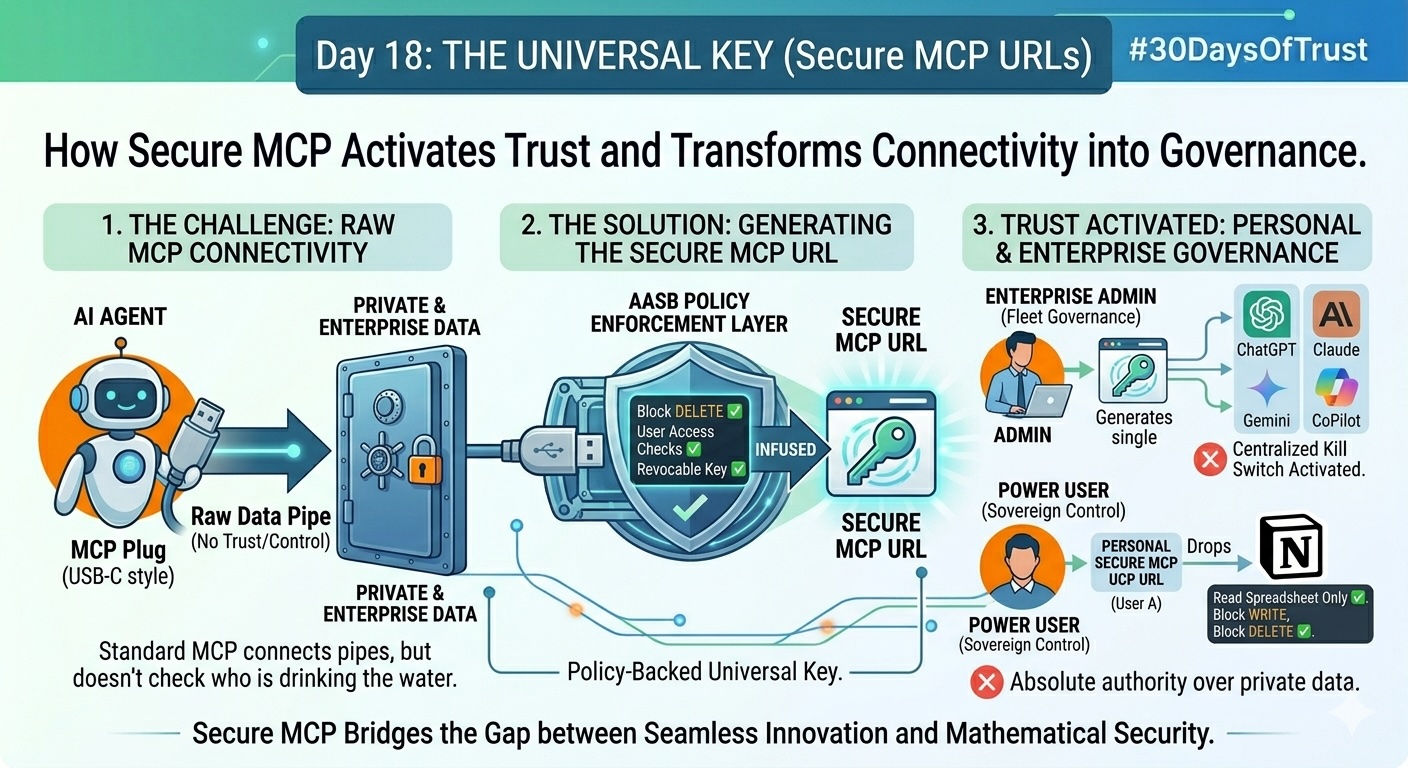
Raw MCP connects the pipes, but it doesn't check who is drinking the water. Discover why Secure MCP is the definitive future of AI security.
Welcome to Day 18 of #30DaysOfTrust.
Yesterday, we discussed the absolute necessity of a "Policy Layer"—an unbreakable rulebook that dictates exactly what an AI agent can and cannot do with your data. But how do we enforce those rules at the actual point of connection?
Earlier in this series, we talked about the Model Context Protocol (MCP) acting as the "USB-C" for AI agents—a brilliant, standardized way to plug AI into any external tool or database.
But here is the hard truth: A universal plug without a security layer is just a fast track for a data breach. Raw MCP connects the pipes, but it doesn't check who is drinking the water.
This is why the future of agentic AI relies entirely on the evolution of this protocol into a Secure MCP.
What Makes an MCP "Secure"? 🔐🛡️
A Secure MCP takes the standard connectivity protocol and wraps it in a zero-trust architecture. Instead of just handing an AI agent an open API key to your database, you generate a Secure MCP URL.
This URL acts as a "Universal Key." But unlike a standard key, this one is smart. It comes pre-loaded with the fine-grained policies we talked about yesterday. It doesn't just grant access; it enforces boundaries in real-time.
Here is how this architectural shift builds trust for different types of users:
Empowering Every Type of User 👥🛡️
-
🏢 The Enterprise Admin: Centralized Trust at Scale
- Imagine an IT Admin trying to secure 500 employees using various AI tools.
- The Vulnerability: If employees manually connect standard MCP servers to company data, the Admin has zero visibility and zero control. It's Shadow AI on steroids.
- The Secure Future: With Secure MCP URLs, the Admin generates specific, policy-backed links for the organization. When an employee plugs that URL into their AI agent, the connection is instantly governed by enterprise rules. The Admin maintains a centralized kill switch, ensuring that the moment a threat is detected, the key is revoked instantly.
-
👤 The Solo Enthusiast: Sovereign Control over Personal Data
- Trust isn't just for massive enterprises. Solo developers and tech enthusiasts connecting personal AI assistants to their private Notion workspaces or local files need the exact same guarantees.
- The Secure Future: A solo enthusiast doesn't want to rely on the AI model's internal safeguards to protect their private life. By using a Secure MCP, they own the gateway. They generate their own secure URL, explicitly stating, "This agent can summarize my financial spreadsheet, but the 'delete' and 'write' tool-calls are strictly blocked."
The Bottom Line 🎯
As AI agents become more autonomous, the way they access our world must become more resilient. We cannot afford to build the next generation of AI infrastructure on open, unmonitored connections.
Secure MCP is the most powerful layer in the Agent Access Security Broker (AASB) stack because it bridges the gap between seamless innovation and mathematical security. It is the definitive future of how we will trust AI with our data.
#30DaysOfTrust #SecureMCP #AASB #AgentSecurity #ZeroTrust #AISecurity #SecuriX #BuildInPublic #AIInfrastructure
Spread the word
Join the Agentic Revolution.
Build secure AI agents with the first-ever Agent Access Security Broker (AASB).
Start BuildingCommunity Forum
Questions, Feedback & Discussions
Join the conversation
Recent Discussions 0 Comments
No questions yet. Be the first!