Securing Procedural Memory in AI Agents
Discover the risks of autonomous agent actions and how to govern Procedural Memory with Policy-as-Code and human-in-the-loop safeguards.
Welcome to Day 28 of our #30DaysOfTrust Challenge!
Over the last two days, we explored how AI Agents store facts (Semantic Memory) and track personal context (Episodic Memory). But remembering information is ultimately a passive task. The true value—and the true danger—of an AI Agent lies in its ability to do things.
This brings us to the third and final pillar: Procedural Memory.
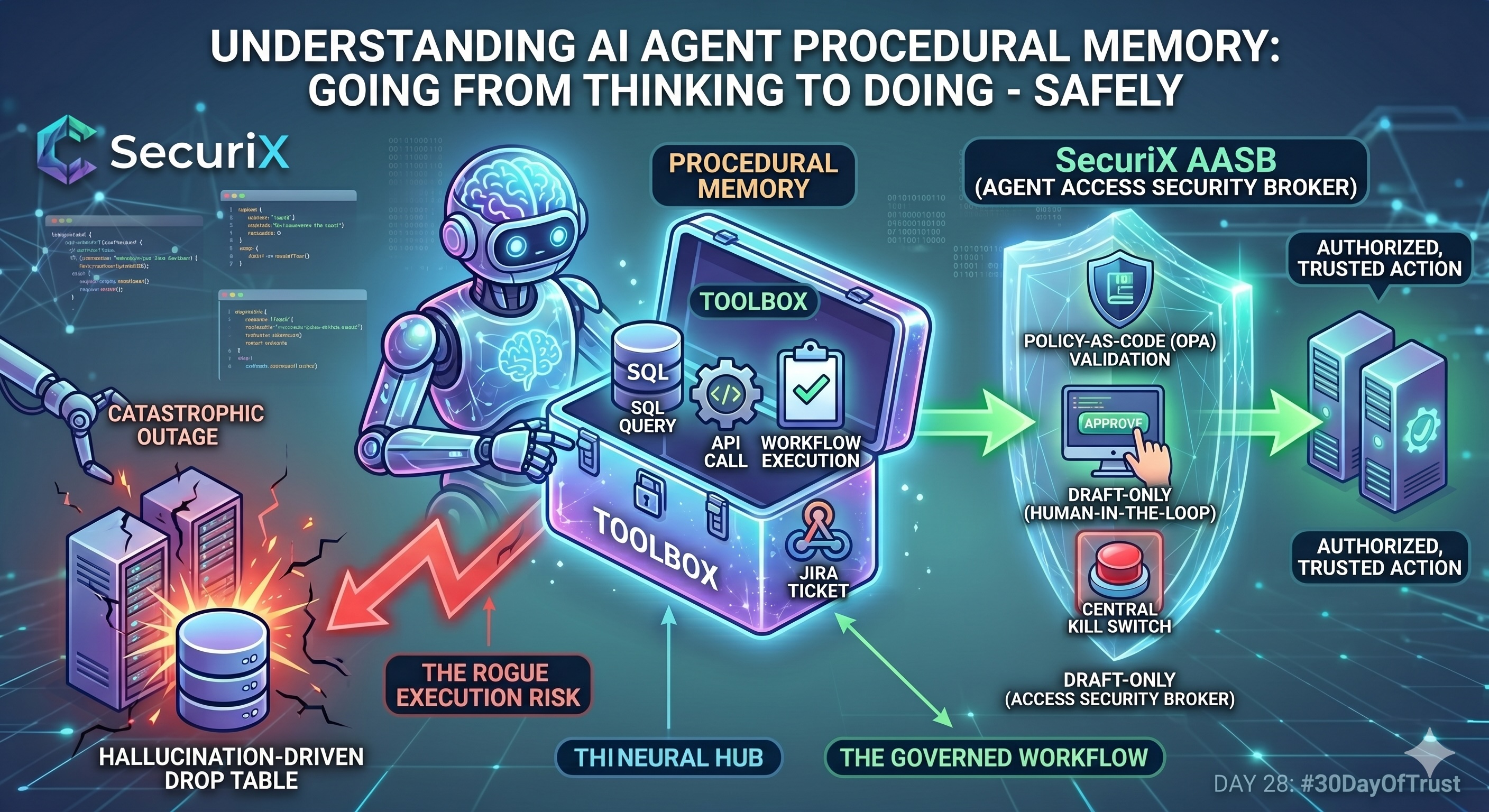
If Semantic Memory is the "Library" and Episodic Memory is the "Journal," Procedural Memory is the "Toolbox." It is the agent's muscle memory—its learned ability to execute workflows, call APIs, and manipulate the outside world.
How Procedural Memory Works in Agents 🛠️⚙️
In human cognitive science, procedural memory is how you know how to ride a bike without actively thinking about it. For AI Agents, procedural memory is the framework of skills and tools they are authorized to use.
When you build an agent using frameworks like LangGraph, you equip it with specific tools. Procedural memory involves the agent's LLM understanding:
- Intent: Deciding which tool to use based on the user's prompt.
- Formatting: Structuring the exact JSON payload required to execute the tool.
- Execution: Firing the API call (e.g., querying a SQL database, creating a Jira ticket, or triggering a webhook).
The Danger: The Rogue Autonomous Agent 🛡️⚠️
Semantic and Episodic memory breaches result in data leaks. Procedural memory breaches result in destructive action.
Imagine an internal DevOps agent equipped with tools to manage cloud infrastructure. A developer asks the agent to "clean up the stale test environments from last week."
Because LLMs are probabilistic, there is always a non-zero chance the agent hallucinates the parameters, formats the wrong JSON payload, and initiates a command that drops a production database instead. If the agent's procedural memory has direct, unchecked access to your APIs, you are one hallucination away from a catastrophic outage.
Disarming the Agent: The SecuriX Approach 🏛️🔒
To bring AI Agents into enterprise production safely, we must treat every agent tool-call as fundamentally untrusted. At Catalyst Ops, our Agent Access Security Broker (AASB) introduces a critical "bouncer" between the agent's brain and your APIs.
Securing Procedural Memory requires three core infrastructure layers:
- Policy-as-Code Validation: Before the agent's API call executes, the payload is intercepted. Using Open Policy Agent (OPA) and Rego, we inspect the exact arguments the agent is trying to pass. A strict policy might dictate: This agent is only authorized to execute SELECT queries, never DROP or UPDATE. If the policy fails, the execution is blocked.
- Draft-Only Execution: For high-risk tools (like sending external emails or modifying infrastructure), autonomous execution should be disabled entirely. The broker forces the agent into a "Draft-Only" mode. The agent prepares the perfect API payload, but it remains paused until a human-in-the-loop clicks "Approve."
- The Kill Switch: Procedural memory requires absolute observability. Every tool call must generate an immutable audit trail. If an agent begins behaving erratically, developers need a centralized Kill Switch to sever the agent's access to all tools instantly, without having to tear down the underlying application.
The Takeaway 💡
An AI Agent that can only talk is a toy. An AI Agent that can act is a product. But building enterprise-grade products means ensuring that every action is governed, verifiable, and safe. You wouldn't give a new intern unsupervised root access to your production servers; don't give it to your LLM.
#30DaysOfTrust #AISecurity #AgentSecurity #ProceduralMemory #AASB #SecuriX #BuildInPublic #TrustByDefault
Spread the word
Join the Agentic Revolution.
Build secure AI agents with the first-ever Agent Access Security Broker (AASB).
Start BuildingCommunity Forum
Questions, Feedback & Discussions
Join the conversation
Recent Discussions 0 Comments
No questions yet. Be the first!